Hit by Ransomware? What a Southern Oregon Small Business Should Do Next

If you’ve turned on a computer in your Grants Pass or Medford office today and found your files encrypted, your shared drives inaccessible, or a ransom note on the screen, you’re facing a ransomware attack. This post walks through the first steps, and — more importantly — what a small business can do to avoid paying the ransom.
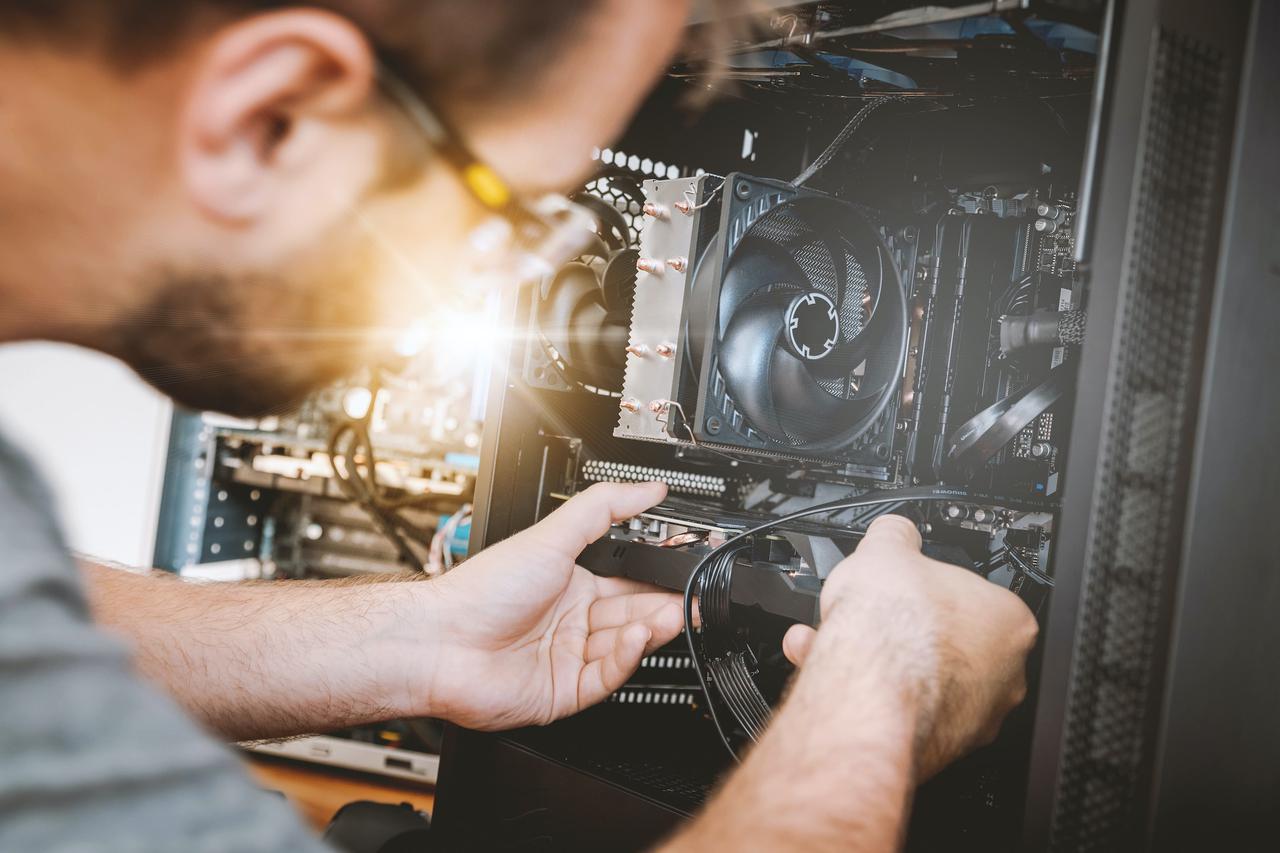
This isn’t something to figure out on your own while the clock is running. Call a trusted local IT provider immediately. But if you’re reading this right now, here’s what to do.
First hour: contain the damage
- Disconnect infected machines from the network. Unplug the ethernet cable or turn off Wi-Fi. Don’t shut the machine down — forensics need the memory state intact.
- Don’t pay anything yet. Ransom payments often fail to restore data, fund further crime, and may be illegal to pay depending on the attacker’s sanctions status.
- Don’t delete anything. You need the encrypted files for possible decryption later.
- Call your IT provider. If you don’t have one, call a local MSP you trust — we answer calls from non-clients in emergencies.
- Preserve the ransom note. Screenshot it. Save the email. The attacker identifier helps with decryption tools.
First 24 hours: assess and respond
- Identify what’s encrypted and what’s clean. This tells you the scope.
- Check your backups. Good offsite backups turn a ransomware attack from an existential threat into a bad weekend. Bad backups turn it into a business-closing event.
- Notify stakeholders. Your cyber-insurance carrier (immediately — many policies have strict notification windows). Your clients if their data is affected. Law enforcement (FBI IC3 at ic3.gov). Possibly Oregon Attorney General and HHS if you’re healthcare.
- Preserve evidence. Don’t wipe anything until the investigation is complete.
Do not pay the ransom if you can avoid it
Paying funds criminal enterprises and — critically — there’s no guarantee you get your data back. Industry statistics consistently show that roughly a third of businesses that pay never get a working decryption key. Even when it works, recovery is slow and incomplete.
The alternative: restore from backup. If your offsite backup is recent and tested, you can rebuild clean without ever touching the ransom demand.
How small businesses end up here in the first place
Almost all ransomware on small businesses starts with one of:
- A phishing email an employee clicked — a fake invoice, a fake DocuSign, a fake IT login page.
- Remote access left exposed — a Remote Desktop port open to the internet with a weak password.
- A vendor with access to your systems got compromised first.
- An unpatched server running an old version of something with a known exploit.
Every one of these is preventable with ordinary, non-exotic managed IT practices.
What prevents this
A managed IT provider serving a Southern Oregon small business should, at minimum, have you running:
- Multi-factor authentication on every account — email, remote access, financial systems.
- Endpoint detection and response (EDR) on every workstation, not just antivirus.
- Immutable offsite backups — backups the attacker cannot reach from inside your network.
- Aggressive patching — workstations and servers updated automatically, not “when we remember”.
- Phishing awareness training — quarterly simulations and periodic refreshers.
- Restricted remote access — no RDP to the internet, ever. VPN or zero-trust access only.
- A written incident-response plan that’s been rehearsed at least once.
If you’re already a client
ITs Managed clients on a managed service agreement have all of the above in place as a matter of course. Our playbook triggers the moment we detect unusual activity — isolate, investigate, notify, restore from backup. We don’t negotiate with attackers.
If you’re not a client yet and you’re under attack now
Call us at (541) 474-6551. We answer real phones, and we’ve helped multiple Southern Oregon small businesses recover from ransomware without paying. The sooner you call, the more we can save.